Besides compliance to banking and regulatory requirements, security is the most important property of banking-grade custody solutions, be it against external attackers or insiders. Providing high security assurance entails multiple and redundant security controls, while mitigating potential components' by following a defense-in-depth approach. Taurus security architecture notably follows the foundational principles of secure systems, as for example described by NSA - see below some of the “general characteristics (..) desirable in a secure system”. In the following, we discuss some of the specific security goals addressed in our design of digital asset custody systems.
#1 Prevent direct access to the seeds or keys
In a hot/warm setting, seeds or keys may be stored in the secure memory of a tamper resistant system. Taurus-PROTECT for example relies on a hardware security module (HSM) certified FIPS 140-2 Level 3, ensuring that any extraction attempt will be detected by the HSM, which would then erase the secrets. Taurus further enhances the HSM security with its own—proprietary and auditable—firmware extension. An alternative approach uses cryptographic secret-sharing and multi-party computation (MPC): with such methods, a key is shared among multiple parties, who run a cryptographic protocol to issue a signature without ever exposing the key. This is suitable when no secure hardware is available, but bears a number of limitations (such as the challenge of securing software-only platforms and reliably running share update protocols).
#2 Prevent unauthorized access to signing capabilities
Even if keys are not exposed directly, an attacker could steal funds by having access to the signing module. A custody solution should therefore enforce multi-party approval, typically on a quorum basis 4 , in a secure environment such as that of a HSM. Blockchain-specific multi-signature may be suitable for selected use cases, but generally blockchain-agnostic solutions prove more reliable and easier to integrate and scale. MPC-based methods directly address this problem by cryptographically preventing access to the key for a single party. However, a downside is then that an authorized quorum of parties can directly sign any transaction and recover the key, bypassing potential security controls regarding transaction content and type.
#3 Prevent unauthorized transactions
Even if access to signing capabilities is restricted to authorized parties following a four-eyes principle, said parties may still request transactions unauthorized by the business rules, be it accidentally or maliciously. To mitigate this risk, business processes and rules must be defined and securely applied for the transactions requested. For example, a secure environment such as that of a HSM can enforce security controls regarding transactions' content and approvers' rights.
#4 Generate keys securely
Key generation is much more than picking a safe pseudorandom generator—this is actually the easiest part. Generating keys, or more accurately the seeds that will be used to derive keys, must be done during a well documented and carefully executed key ceremony, during which back-up values are also created, tested, and sealed.
#5 Ensure reliable back-ups
A custody solution with the best cryptography and secure hardware is pointless if someone has access to back-ups of the keys, or if the back-ups will not work when needed. This suggests that back-ups should 1) be subject to shared control, for example via threshold secret-sharing mechanisms, 2) be thoroughly tested during the key ceremony, 3) be stored in tamper-evident containers and regularly checked for tampering, and 4) be subject to tested recovery processes and technical procedures, in order to ensure business continuity in the expected time.
#6 Protect logs and databases
Like any modern computerized service, a custody solution generates extensive logs, and performs read and write operations in a database. Database content should be encrypted when relevant (for example if PII 5 data is stored), and the integrity of its content should be protected. Likewise, the integrity of logs is particularly important in order to ensure that any unauthorized operation cannot be erased from the recorded history.
#7 Maximize solution auditability
To ensure a high security assurance, a custody solution should not be a complete black-box. Instead, it should provide a fair amount of transparency regarding its internal logic (for example, by sharing its source code with its users), and regarding its activity (via logs generated by its various components). Control and auditability of the solution is essential in the context of compliance audits, security audits, change management, and incident response processes. The more the provider masters the technology stack, the less opaque/black-box the solution is. Audit reports from reputable third parties should be available to users of the solution.
#8 Ensure supply chain and build integrity
The provider of a custody solution must be able to provide guarantees that the software running in the custody solution, be it on-premise or as a service provider, corresponds to the components provided for audit and cannot be modified during its operation. Such guarantees require a combination of technology (such as continuous integration and authentication tools) and procedures (in terms of change management and role segregation).
Key take-away:
Ask your providers what components of the value chain they control, vs. outsourced ones. The highest premium and value shall be given to those who master the full technology stack including the development and management of cryptographic functions, which represent, in our view, the heart of the nuclear plant. This provides the highest assurance against technology obsolescence – we have seen several providers that assemble this module not being able to cope with technology progress and their clients decide to switch. In other words, identify the builders from the assemblers who outsource the heart of the nuclear plant. At Taurus, we build.

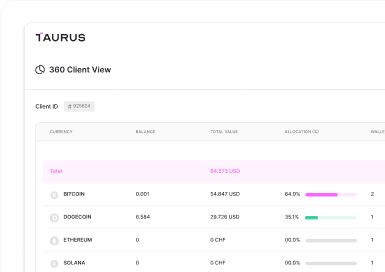






 Taurus-PROTECT Custody
Taurus-PROTECT Custody
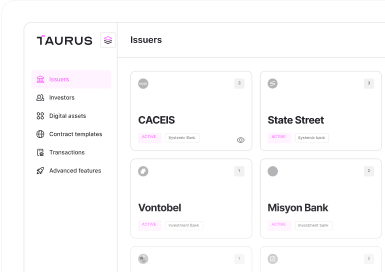
 Taurus-CAPITAL Tokenization
Taurus-CAPITAL Tokenization
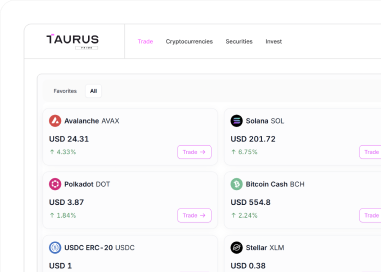
 Taurus-PRIME Trading
Taurus-PRIME Trading
 Taurus-NETWORK Collateral
Taurus-NETWORK Collateral
