For every complex problem there is an answer that is clear, simple, and wrong.
—H. L. Mencken
When we talk about crypto assets, custody means the safekeeping and management of these assets. This involves ensuring the confidentiality, integrity, and accessibility of the cryptographic keys that underlie the respective blockchain entries of these assets. Custody’s security is essential because if the keys are lost, then the funds are lost forever—except for certain tokenized assets.
A custody model is the strategy picked to handle this custody. It is a multi-faceted concept, whose features should align well with each organization’s operating model and risk management. Let’s delve into its three main dimensions.
Self-custody or sub-custody?

Image AI-created using Midjourney
The main decision is between do-it-yourself and delegation, or in other words:
-
Self-custody is when you keep full control of the assets—only you know the keys, thus you don’t need to trust a third party. But with that control comes responsibility. You’re in charge of defining and executing all security procedures, and only have yourself to blame if things go wrong. People often say “not your keys, not your coins” to advocate for this approach, but let’s not forget the counterpart: “lose your keys, lose your coins”.
-
Sub-custody is about placing your trust in an organization specialized in digital asset custody. They’ll store your funds and provide means for you to manage them—such as initiating transfers via a web interface. When going this route, it is imperative to do your due diligence and assess the risk properly. For instance, how likely is the custodian to go bankrupt? What kind of internal controls reduce the “insider risk”? You are dealing with the counterparty risk.
Deciding between self-custody and sub-custody hinges on your unique situation. If you’re a bank or large corporation, self-custody is usually the way to go since storing and managing assets is your bread and butter. You have the core capabilities, along with the know-how in risk regulations and auditing protocols. If you’re a financial services firm such as an investment fund or a broker, self-custody is recommended provided you have the right staff, expertise, and overall readiness to manage a custody system.
But remember that self-custody does not mean reinventing the wheel and building your own custody tech. Instead, apart from rare exceptions, those doing the self-custody route lean on third-party solutions, such as Taurus-PROTECT. Self-custody eliminates the counterparty risk, enables you to control your product roadmap, ensures privacy (as opposed to a sub-custodian seeing all flows) while optimizing your business case thanks to higher margins.
If you’re an individual or a smaller, less-regulated outfit, sub-custody may be a better option from a risk management perspective. Just ensure you’re partnering with a reliable sub-custody provider. In the volatile and partially regulated cryptocurrency space, choosing such a provider can be tricky (post-FTX and beyond).
Lastly, there’s hybrid custody. This describes models where control of keys is distributed among multiple parties—typically the funds' owner and a service provider—via multi-party signing protocols. In such cases, only the owner (client) maintains full control of the funds via their back-up recovery values. Multi-signature models also fall under the hybrid category, as governance and control of the funds is cryptographically enforced and no single entity can unilaterally initiate transactions.
Hot or cold?

Image AI-created using Midjourney
Loosely speaking, a hot wallet is a custody system easily accessible and directly connected to the internet, whereas a cold wallet is offline and involves more manual steps, making it safer against theft, notably software vulnerabilities and phishing.
At Taurus, our custody solution Taurus-PROTECT supports various “temperature models”, which we generally define as follows:
-
Hot: Transactions can be automatically performed via API, involving one or multiple systems as approvers via quorum-approval models.
-
Warm: Transactions need the manual approval of human parties. These endorsements are transmitted to a secure environment that verifies them and creates the blockchain transaction and broadcasts it to the network.
-
Cold: The environment holding the keys is physically disconnected from any computer network. It thus requires hands-on intervention—following the right approvals and access procedures—prior to finalizing a transaction.
With Taurus-PROTECT, in all these setups, the master keys, or “seeds”, are stored in hardware security modules (HSMs) whose secure memory offers high security assurance against various classes of attacks, including physical attacks (thanks in part to their FIPS 140-2/3 certification).
In addition to these three models, “cryogenic” setups might use purely non-digital systems to stow away keys in safe locations. Such approaches can protect against theft but may be deceptively risky and more akin to “security theater” than reliable storage if the equipment is poorly chosen or if procedures are inadequate—particularly as time rolls on and different persons get involved.
A challenge when juggling varied wallet temperatures is managing fund distribution. How much to hold on each wallet type? A rule of thumb is to have the overwhelming majority of funds in cold storage, and only enough on hot and warm for day-to-day operations, with a buffer sufficient to handle withdrawal peaks. Processes must be in place to shuffle funds between wallet types, execute emergency transfers from cold (for example, as a stop-loss mechanism), and retrieve back-ups from each wallet type (especially the frostier ones).
Pooled or allocated?

Image AI-created using Midjourney
Last, and maybe least, let’s tackle the question of funds pooling. If you’re a bank managing your clients' assets, then you have two main options:
-
Pooled model, wherein all assets under custody are stored in the same “bucket”, such as the same Bitcoin address for bitcoins. In this setup, similar to an omnibus account, the bank maintains an internal record of each client’s balances. For example, if the pooled address contains 10 bitcoins, the bank’s records database may show: “Alice: 3 bitcoins; Bob: 0.5 bitcoins; Mallory: 2 bitcoins; and so on”, along with a ledger of the transactions history. Most cryptocurrency exchanges operate this way.
-
Allocated model, wherein the funds of a given client are assigned to distinct addresses, and therefore segregated from each other. Following our earlier example, the bank would have distinct Bitcoin addresses for Alice, Bob, Mallory, and all other clients. These addresses might be generated in two ways: 1) all the addresses belong to the same “tree of addresses”, that is, can they all be derived from the same seed, and 2) addresses' private keys are completely independent of each other, thus can be completely segregated.
Each model carries its own set of legal nuances, risk considerations, and operational constraints. Many variants exist beyond these two simplistic models, with their design and features shaped by the custodian’s activity and the idiosyncrasies of each blockchain and asset type. For details, please refer to CMTA’s Digital Assets Custody Standards (DACS) in §2.2.
(Note that such “pools” are entirely different from mining pools.)
Closing thoughts
Image AI-created using Midjourney
Whichever model best suits your organization, its security level can swing from the best to the very worst based on how rigorously you handle its risks.
From what we’ve seen, a frequent oversight is downplaying the risk of losing (access to) funds compared to theft risks. Countless individuals and organizations have purchased expensive, “ultra-secure” products, only to lose their assets due to subpar back-ups or inadequate testing thereof.
For financial institutions, the most secure custody solution will be a self-custody system that boasts:
-
Trustworthy technology from a reputable provider offering “battle-tested solutions".
-
Comprehensive risk management, encompassing governance, security controls, and audit considerations.
To learn more about our approach to custody models, please do not hesitate to contact us.

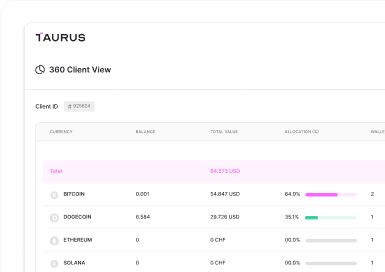






 Taurus-PROTECT Custody
Taurus-PROTECT Custody
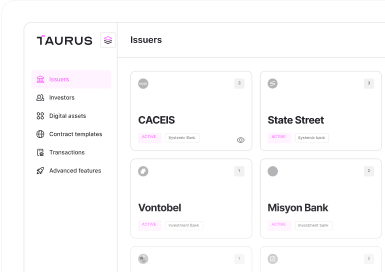
 Taurus-CAPITAL Tokenization
Taurus-CAPITAL Tokenization
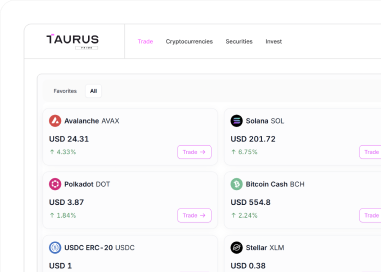
 Taurus-PRIME Trading
Taurus-PRIME Trading
 Taurus-NETWORK Collateral
Taurus-NETWORK Collateral
