The Bank for International Settlement (BIS) recently announced Tourbillon, a prototype of a CBDC (Central Bank Digital Currency) with unique privacy features, providing a level of anonymity comparable to that of cash. Taurus contributed to this project by reviewing its cryptography and security architecture, an opportunity extended to us by the Swiss National Bank (SNB), which championed this project.
To begin, we will provide a brief overview of CBDCs and the associated privacy concerns. Then, we’ll focus on the Tourbillon CBDC prototype, specifically examining its cryptographic cornerstone—blind signatures.
Privacy concerns around CBDCs
CBDCs represent a digital iteration of a nation's fiat currency, issued and regulated by its central bank. In contrast to decentralized cryptocurrencies like Bitcoin or Ethereum, CBDCs operate within a centralized and regulated framework. Despite their potential benefits, such as improved payment efficiency, reduced transaction costs, and broader financial inclusion, CBDCs bring about significant concerns, particularly in the realm of privacy and surveillance.
Privacy concerns arise from the potential for CBDCs to enable unprecedented levels of financial surveillance. With digital currencies, central banks could, in theory, have real-time visibility into all transactions. This raises questions about the extent to which governments should have insight into the private financial dealings of individuals.
Privacy, in this context, entails the right to keep personal information confidential, restricted to a trusted group of individuals. This concept acknowledges varying levels of privacy:
-
confidential transactions, where personal information is visible only to trusted parties (e.g., credit card payments)
-
pseudonymous transactions, where identifiers or public addresses can potentially identify an individual (e.g., bitcoin transactions)
-
anonymous transactions, where the parties involved remain unidentified (e.g., cash payments).
Balancing individual privacy protections with the imperative to combat illicit payments is a significant challenge. It requires careful consideration of individual privacy protections with broader public policy objectives, especially in the realms of anti-money laundering and combating the financing of terrorism (AML/CFT) and countering tax evasion.
Tourbillon’s CBDC privacy goals
The Tourbillon project attempts to address the privacy and surveillance concerns by outlining specific requirements for the visibility of transaction data, as exposed in the Tourbillon report (§3.1, emphasis added):
“Project Tourbillon shows that it is feasible to implement a CBDC that provides payer anonymity while combating illicit transactions. In particular, a consumer paying a merchant with CBDCs is anonymous to all parties, including the merchant, banks and the central bank. However, the identity of the merchant is known to the payer and is only disclosed to the merchant’s bank as part of the payment and is kept confidential thereafter. The central bank does not see any personal payment data but can monitor CBDC circulation at an aggregate level. (…) Tourbillon shows that central banks can monitor the aggregate use of CBDCs in real time without seeing any personal information.“
Achieving this goal is particularly challenging, as the Central Bank must indeed be able to detect illicit transactions, prevent counterfeit money, and generally protect all parties involved (including consumers), in accordance with applicable laws and regulations.
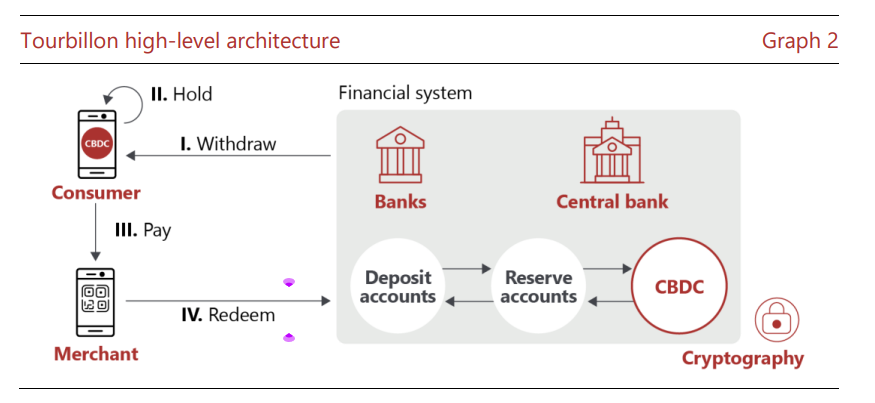
Source: Tourbillon report (§2.1).
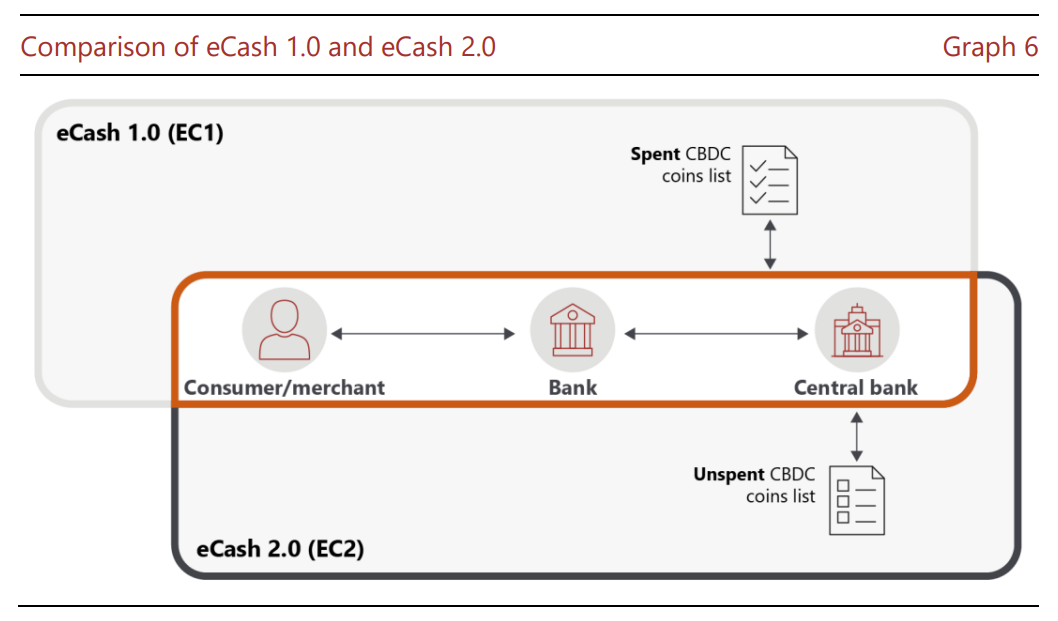
To achieve these goals, BIS proposes two models, eCash 1.0 (EC1) and eCash 2.0 (EC2), supposedly a tribute to Chaum’s 1982 Ecash model, which relied on similar cryptography as BIS's prototype. Both protocols use blind signatures (which we’ll explore later). The main difference between the two lies in the timing of recording CBDC unique identifiers—in EC1, the Central Bank records CBDC unique identifiers upon redemption, whereas EC2 records them upon issuance. To make this second case work, EC2 needs to be equipped with another fascinating cryptography component, mix networks.
Finally, it’s worth noting Tourbillon does not rely on blockchain technology at all.
Cryptographic magic: Blind signatures
“When a software engineer says it’s impossible, that just really means it’s cryptographically interesting.”—Moti Yung
Tourbillon’s key cryptography trick is a concept known as blind signatures, a notion first proposed in 1982 by David Chaum. The idea behind blind signatures is quite simple but powerful. In a standard digital signature scheme such as ECDSA, the signer knows the message signed, and thereby, knows what they are endorsing. However, there are situations where it is desirable for the signer not to know the message they are signing. This is where blind signatures come into play.
A blind signature works as follows:
1. Blinding the message: The person who wants to receive signature first "blinds" the message. This is typically done by applying a random, secret mask to the message. The masked message is then sent to the signer. The key here is that the masked message is transformed in such a way that the signer cannot discern its original content.
2. Signing the message: The signer then signs the blinded message without seeing its actual contents. This signature, due to the mathematical properties of the blinding process, is still valid for the original, unblinded message.
3. Unblinding the signature: The original sender of the message then removes the blinding mask, revealing the original message with a valid signature that can be verified by anyone.
In Tourbillon’s prototypes, blind signatures are instrumental in preserving payers' privacy by ensuring that no entity, including the Central Bank, can link the spending history of a coin to the identity of the payer. The Central Bank signs the coins, confirming their legitimacy and thereby preventing counterfeits. However, the bank only gains knowledge that some coin was issued by a specific payer but won’t know which one.
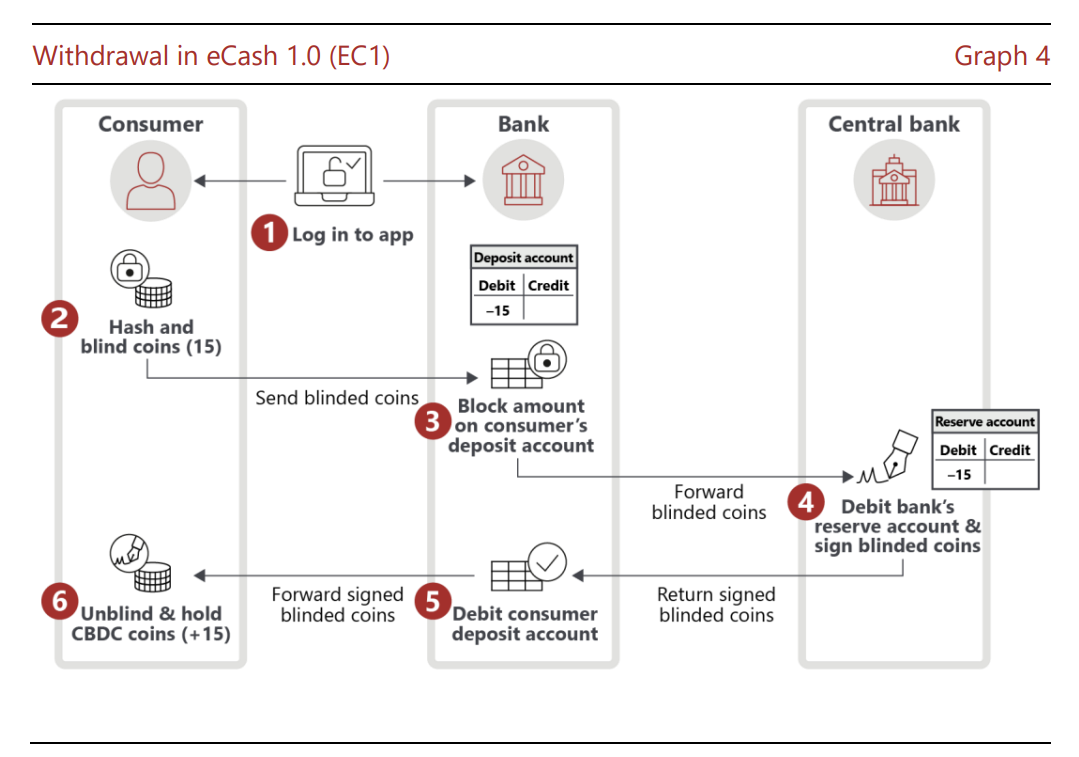
Concretely, as illustrated below, a payer would obtain CBDC from the Central Bank via their bank after:
1. creating coins with random (unpredictable) IDs
2. blinding them using random masks
3. sending these coins for signature to the Central Bank via the Bank and proper authentication and authorization mechanisms
4. receiving the signed coins and unblinding them, making them ready for payments to some merchant.
Example of blind signature: RSA cryptosystem
The simplest example of blind signature, as proposed by David Chaum 40 years ago, is based on the RSA cryptosystem. Given a message m to be signed, the payer picks a random number r and computes m' = mre mod N, where e is the public exponent of the signer (that is, the Central Bank), and N is the associated modulus. When signing m', the Central Bank will produce s' = (mre)d = mdr mod N, since ed = 1 mod φ(N). The payer can then divide s' by r to obtain md mod N, the final, unblinded signature.
Here, it's important to note that, as with general RSA-based signatures, m may not directly represent the application data but could instead be an encoding of the message as per the PSS standard.
However, the Tourbillon project does not use RSA. Instead, it employs a lattice-based signature scheme, providing post-quantum security, unlike RSA.
To learn more about CBDCs and privacy aspects, you may consult these pieces from the European Central Bank working paper, from BIS, from the World Economic Forum (and a second one from 2021).

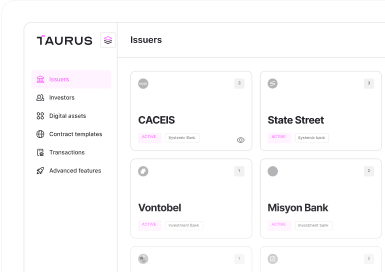






 Taurus-PROTECT Custody
Taurus-PROTECT Custody
 Taurus-CAPITAL Tokenization
Taurus-CAPITAL Tokenization
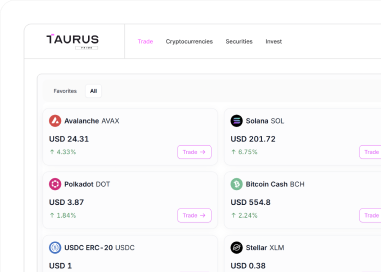
 Taurus-PRIME Trading
Taurus-PRIME Trading
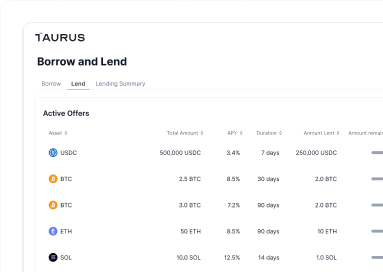
 Taurus-NETWORK Collateral
Taurus-NETWORK Collateral
